Vehicle architecture is rapidly evolving into software-defined platforms that are continuously updated via OTA, connected to cloud ecosystems, and increasingly powered by AI-driven functionality. Most critically, mobility infrastructure now evolves post-deployment, with trust boundaries shifting dynamically across in-vehicle networks, backend systems, and third-party integrations.
To maintain security in these continuously evolving systems, automotive cybersecurity engineering has had to evolve. In response, the industry has progressed through three distinct stages: Cybersecurity Engineering, DevSecOps and AI-Defined DevSecOps.
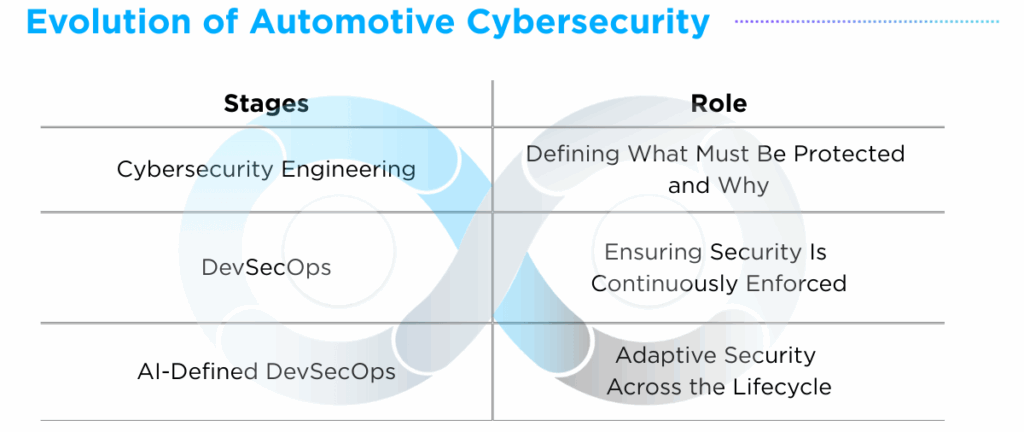
Cybersecurity Engineering: Defining what must be protected and why
The first stage begins with Cybersecurity Engineering, which defines what components must be protected and why. Security is structured as engineers identify critical assets, define potential threats, assess risk levels, and design appropriate mitigations. This process transforms abstract security concerns into formalized risk models and enforceable security requirements.
Cybersecurity Engineering spans the full vehicle ecosystem. Within the vehicle, it covers embedded systems such as ECUs and domain controllers, as well as in-vehicle communication networks including CAN and Automotive Ethernet. Across the software lifecycle, it governs secure boot, firmware integrity, and over-the-air (OTA) validation mechanisms to ensure software authenticity. Beyond the vehicle boundary, it addresses V2X authentication, vehicle-to-cloud APIs and secure backend communications.
Core outputs include asset identification, threat modeling, Threat Analysis and Risk Assessment (TARA) and risk classification. These activities enable compliance with global standards such as UNECE R155 and ISO/SAE 21434, forming the backbone of Cybersecurity Management Systems (CSMS).
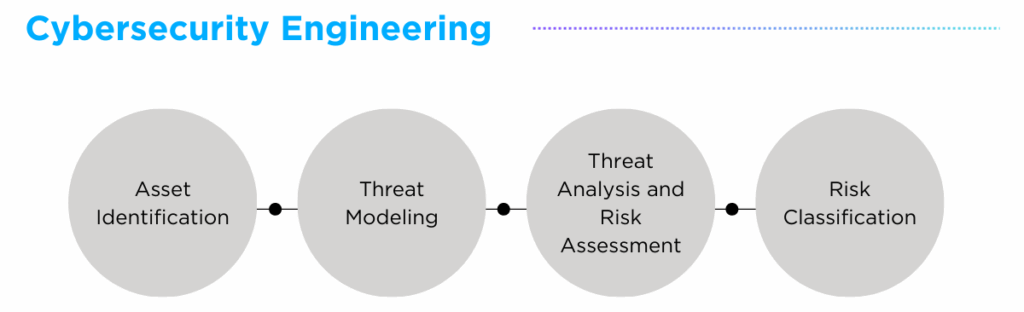
Industry implementations such as AutoCrypt CSTP (Cybersecurity Testing Platform) (Link) and TARA consulting services (Link) reflect the scope of this layer, combining regulatory alignment frameworks with technical validation practices that strengthen risk modeling across OEM and supplier environments.
Cybersecurity Engineering defined what required protection, but it did not ensure that protection would keep pace with change. Risk models were built on the assumption of relative architectural stability, and validation occurred at scheduled intervals. As vehicles became continuously updateable and trust boundaries shifted dynamically, periodic enforcement was no longer sufficient. Security logic had to move beyond definition, marking the transition to DevSecOps(Development, Security, and Operations).
DevSecOps: Ensuring Security is Continuously Enforced
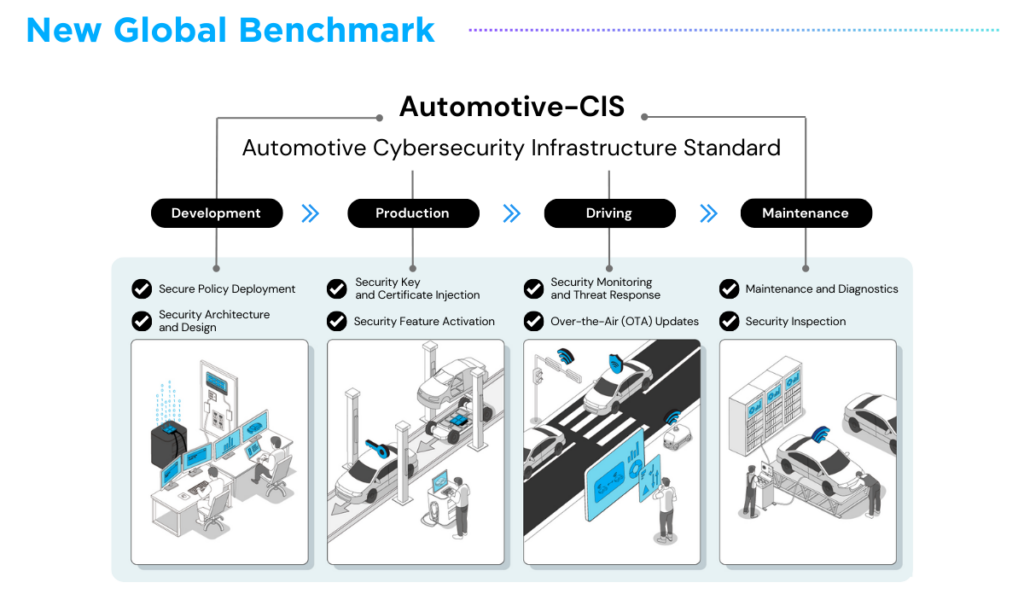
As vehicle architectures evolved beyond static release cycles and periodic validation, security controls had to be embedded directly within development and deployment workflows.
DevSecOps — a software engineering framework that integrates security into development and operational processes — emerged to address this requirement. Rather than treating security as a downstream validation step, DevSecOps embeds automated security controls into CI/CD pipelines to ensure continuous enforcement throughout the vehicle software lifecycle.
Security testing became integrated into automated build processes, resulting in faster validation cycles and improved audit readiness. Secure build templates reduced configuration errors, firmware signing workflows were automated, and key provisioning systems became embedded into production processes. Defined security requirements became programmatically enforced, ensuring traceability at scale.
AUTOCRYPT’s launch of Automotive-CIS (Cybersecurity Infrastructure Standard) (Link) supports this stage by providing a unified framework for lifecycle governance through the integration of CSMS, SUMS, vSOC and TARA. This enables security activities to remain aligned across development, production and operational phases, strengthening end-to-end lifecycle consistency.
While Stage 2 marked a significant evolution in continuous enforcement, it retained a critical assumption: that the underlying risk model remained valid. DevSecOps enforces predefined controls, but it does not inherently detect when architectural changes invalidate original risk assumptions. In environments where OTA updates introduce new communication paths and AI models evolve post-deployment, risk landscapes shift dynamically. In such conditions, continuous enforcement must evolve into adaptive intelligence, paving the way for AI-Defined DevSecOps.
AI-Defined DevSecOps: Adaptive Security Across the Lifecycle
If Stage 1 defined security logic and Stage 2 automated its enforcement, Stage 3 introduces intelligence into the lifecycle.
AI-Defined DevSecOps addresses the core limitation of rule-based automation by continuously assessing system state, detecting architectural change, and validating whether existing risk assumptions remain relevant. Rather than simply enforcing predefined controls, this stage enables adaptive orchestration, ensuring security mechanisms evolve alongside system behavior.
At this stage, security becomes a closed-loop adaptive system. When an engineering change occurs, the system performs automated risk impact analysis, recalculates risk, triggers required revalidation and regenerates compliance evidence. In doing so, it ensures that the impact of changes is assessed in real time and that enforcement mechanisms remain synchronized with evolving architectures.
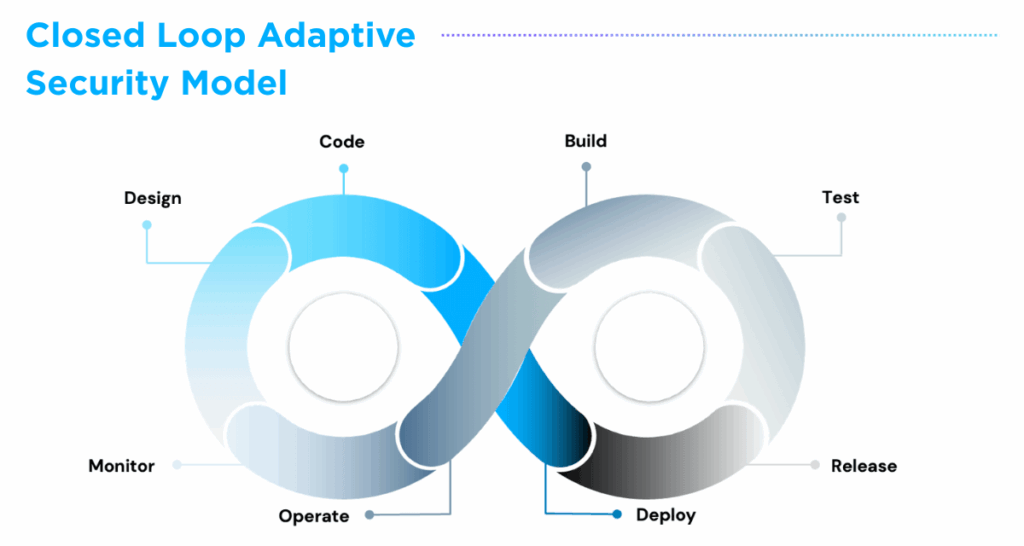
AUTOCRYPT’s advancements in AI-Defined DevSecOps, first introduced at CES 2026 (Link) — including AI-powered TARA automation and automated test case generation within AutoCrypt CSTP — demonstrate this evolution in practice. By enhancing threat modeling completeness and deepening validation coverage within DevSecOps pipelines, these capabilities elevate security from automated enforcement to intelligent lifecycle orchestration.
As mobility ecosystems are no longer fixated at design time, adaptive security becomes a structural necessity. In this environment, AI-Defined DevSecOps is not merely an enhancement, but a foundational layer for securing next-generation mobility systems.
Evolutionary Stages of Automotive Cybersecurity Engineering
Automotive cybersecurity engineering has evolved from structured risk definition to automated enforcement and now toward intelligent adaptation.
As automotive systems become increasingly intelligent, the security layer must become equally intelligent. Adaptive security is foundational in next-generation mobility, where architectures shift dynamically and AI-driven functionality evolves over time.
AUTOCRYPT is committed to proactively expanding AI-Defined DevSecOps across its portfolio, strengthening adaptive cybersecurity infrastructure as a core pillar of its research and development. Through this approach, we support OEMs and Tier 1 suppliers in maintaining continuous, resilient protection across rapidly evolving mobility ecosystems.
To learn more about our end-to-end mobility solutions, visit https://autocrypt.io/


![[AUTOCRYPT] CES 2026 Highlights](https://www.autocrypt.io/wp-content/uploads/2026/01/12_8-D-30_2-est-2.png)

