In-Vehicle Systems
AutoCrypt IDS
Intrusion detection system for vehicular environments

Intrusion detection and policy management for in-vehicle systems.
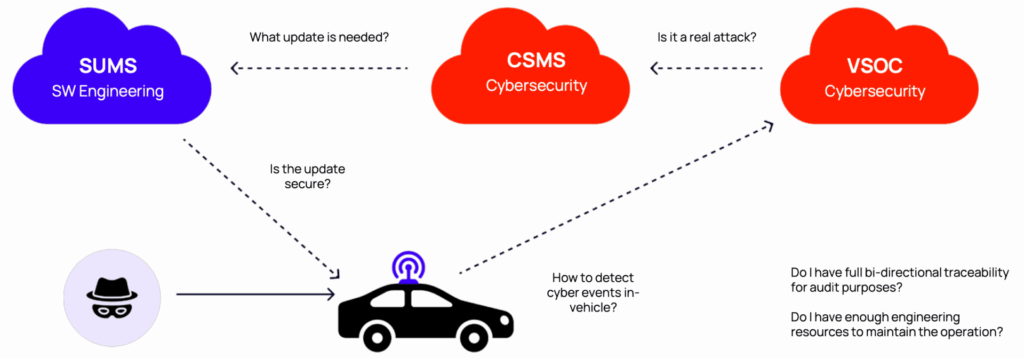
To counter cybersecurity threats, UN Regulation R155 requires all automotive OEMs to have a cybersecurity management system (CSMS) in place. To establish an effective CSMS, an intrusion detection system (IDS) and vehicle security operations center (vSOC) are crucial.
AutoCrypt® IDS provides a vehicular intrusion detection solution that detects, filters, and prevents cyberattacks against in-vehicle systems. It consists of an N-IDPS (network intrusion detection and prevention system) and an H-IDS (host intrusion detection system), complemented by event reporting, automated policy generation and simulation, and ECU resource optimization.
AutoCrypt® IDS can be easily integrated into both AUTOSAR and legacy environments. It can be linked to AutoCrypt® vSOC or third-party vSOCs.
Overview
AutoCrypt IDS security architecture
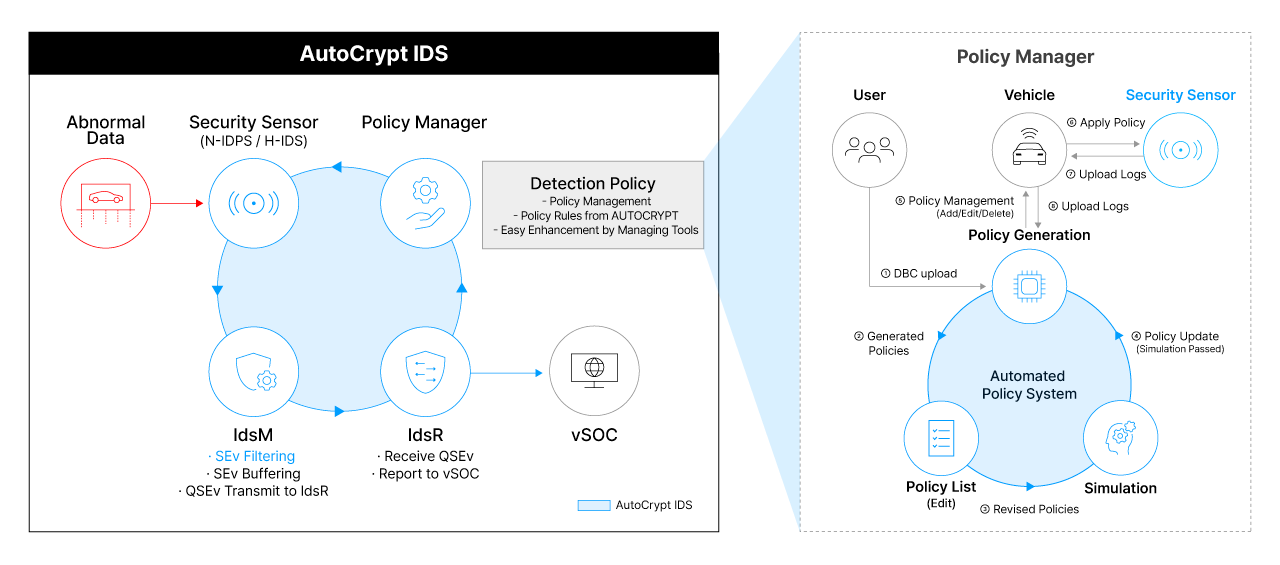
AutoCrypt® IDS is centered around AUTOCRYPT’s proprietary Security Sensor, which uses an N-IDPS to detect abnormal data in the network, and an H-IDS to identify any abnormal behaviours of the ECUs. The IdsM (Intrusion Detection System Manager) evaluates detected security events (SEv) and sends qualified cases (QSEv) to the IdsR (Intrusion Detection System Reporter), which reports them to the vSOC.
Besides intrusion detection, AutoCrypt® IDS also ensures its Security Sensor is up-to-date with the latest attack patterns and threats. The IdsR reports newly discovered security incidents to the Policy Manager, which utilizes data from the DBC (CAN database files) to automatically generate, simulate, and apply new policies to the Security Sensor.
AutoCrypt® IDS offers easy architectural integration for both AUTOSAR and legacy environments, applicable in both traditional microcontrollers (MCU) and more advanced application processors (AP).
Highlights
Efficient, automated, and optimized IDS
Smart Policy Simulator
- Runs simulations to evaluate detection policy effectiveness
- Suggests policy improvements based on the order of importance to vehicle functions
- Extremely low false detection rate
ECU Resource Optimization
- Generates a preview of policy file size and remaining ECU storage space
- Depicts storage usage rate in real-time
- Enables easy tracking of policy files based on size
- Suggests similar policies that consume less resources
Automated Policy Generator
- Automatically updates detection policies by analyzing the DBC (CAN database files)
- Applies updated policies to Security Sensor
- Systematically applies policies to specific ECUs and CAN buses
- Real-time updates ensure protection against latest threats
Efficient Security Sensor
- Accurately detects anomalies in the system and network and reports security events (SEv) to the IdsM
- Evaluates all in-vehicle software and system resources in real-time for timely detection
- Readily implementable in both AUTOSAR and legacy environments
- Adapted to ensure basic car controls remain uninterrupted
Case Study
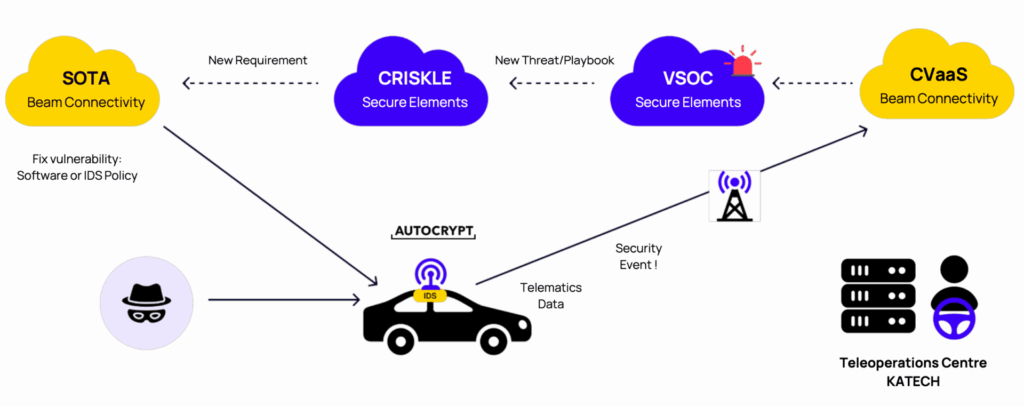
SecureTCU Korea-UK Collaborative R&D Project
Project Overview
Title: SecureTCU (Link)
Overview: An Integrated TCU, IDS, OTA and CRISKLE-Based Platform for Continuous Cyber Compliance
Objective: Develop and demonstrate an integrated platform that enables continuous, cost-effective cybersecurity compliance with UNECE R155/R156 and ISO/SAE 21434, while supporting rapid response to cyber incidents in connected vehicles
Duration: December 2023 ~ October 2026
Roles and Contributions
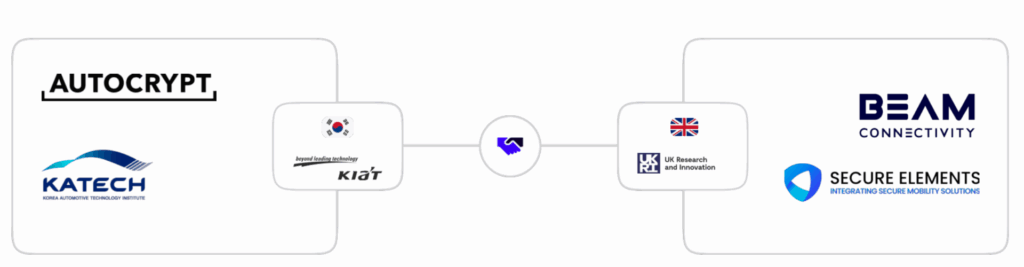
South Korea
Ministry of Trade, Industry and Energy (KIAT)
- Project coordination and funding authority
AUTOCRYPT
- IDS stack integration on the TCU for real-time threat detection
- Rule Generator and Policy Validator for CAN, cellular, and host-based IDS policy management
- Cryptographic protection and trusted delivery of security event messages
Korea Automotive Technology Institute (KATECH)
- Vehicle integration, testing, and solution validation through simulated cyberattack scenarios
- Real-world pilot demonstration using a remote driving system to validate the integrated solution under operational scenarios
United Kingdom
Innovate UK
- Project coordination and funding authority
Beam Connectivity
- TCU architecture design and development
- Development of the Connected Vehicle-as-a-Service platform
- Implementation of connectivity, telemetry, remote management, and OTA update functions
Secure Elements
- Development of the CRISKLE platform to support CSMS and SUMS
- Provision of TARA-based analysis, compliance assessment, MSOC-driven threat monitoring and operational orchestration, and full traceability for cybersecurity and A-SPICE audits
Our Approach to the Challenge
Challenge: Detection and rapid response to cyber incidents in connected vehicles
Solution: An integrated platform for proactive detection and response, significantly reducing response time and compliance costs