UN R155 is widely regarded as a critical compliance milestone for OEMs and Tier suppliers under the UNECE WP.29 framework. Without a certified Cybersecurity Management System (CSMS), vehicles cannot obtain type approval in contracting markets, making compliance essential for market access. By contrast, comparatively less attention has been given to the EURO 7 standards — EU’s latest vehicle emissions and durability regulatory framework set to begin application from November 2026.
The EURO 7 standards, embedded within Regulation (EU) 2024/1257 (Link) is commonly viewed as an environmental regulation introducing new pollutant limits, battery performance thresholds, anti-tampering provisions and lifecycle monitoring requirements under the EU type-approval framework. However, its significance extends beyond conventional emissions compliance and should be understood within an integrated regulatory architecture alongside UN R155.
This blog post aims to clarify why EURO 7 does not operate independently of WP.29 cybersecurity requirements and why, in practice, it functions as a structural reinforcement of vehicle type-approval obligations. Understanding how EURO 7 strengthens the operational relevance of UN R155 is essential to safeguarding type approval within an increasingly interconnected regulatory environment.
I. Understanding EURO 7
Role of the EURO Series in the Automotive Industry
The EURO regulatory framework has historically played a defining role in shaping automotive engineering priorities across Europe. From its earliest iterations, its core objectives have centered on reducing harmful pollutants, protecting public health and air quality, and providing predictable compliance pathways for manufacturers operating within the European market.
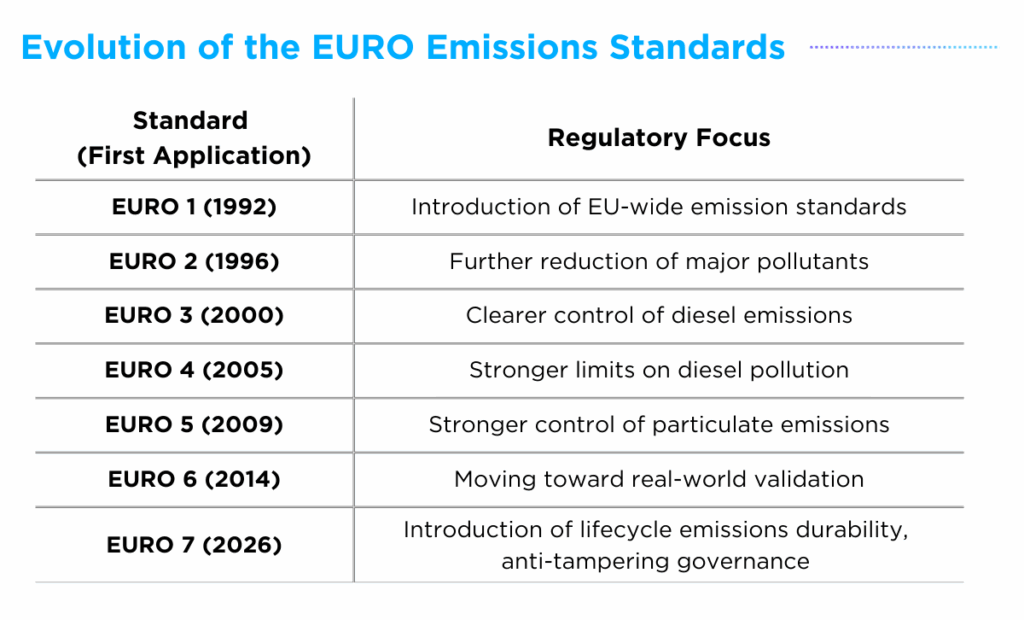
From EURO 1 through EURO 6, each iteration progressively tightened emissions limits, expanded testing methodologies, and increased alignment with real-world driving conditions. However, despite these advancements, the underlying regulatory logic remained largely certification-based and event-driven. Vehicles were validated under defined laboratory and real-driving emissions (RDE) test conditions, and once type-approval was granted, they were presumed compliant unless defects emerged during operation.
Transition from EURO 6 to EURO 7
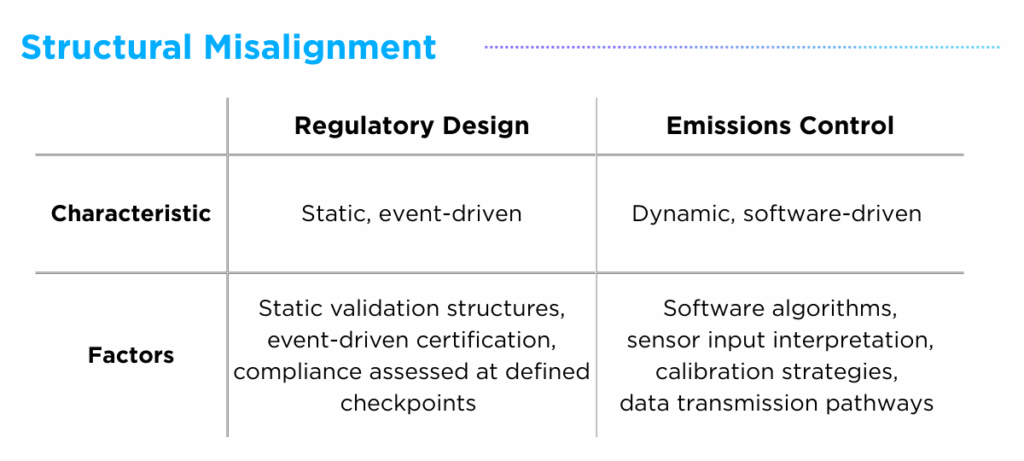
Up until EURO 6, the standards were designed to evaluate predominantly mechanical vehicle architectures, where emissions behavior was largely hardware-determined and relatively stable over time. The turning point came with the Dieselgate corporate scandal, in which automakers engaged in the large-scale, deliberate use of defeat devices to manipulate emissions testing outcomes. Although vehicles passed defined regulatory testing conditions, their emissions performance diverged under real-world driving conditions, exposing the vulnerability of a certification-centered regulatory model.
This incident revealed a structural misalignment between regulatory design and vehicle behavior, where compliance was assessed in a static manner while modern emissions performance had become dynamic and increasingly software-driven.
II. EURO 7 within the WP.29 Cybersecurity Architecture
How EURO 7 Reflects the Software-Defined Nature of Modern Vehicles
EURO 7 redesigns the regulatory architecture to reflect the software-defined nature of modern vehicles, recognizing that emissions behavior can be influenced by software logic and data modifications occurring throughout the vehicle lifecycle.
Through amendments to Regulation (EU) 2018/858 (Link) Article 84, EURO 7 explicitly incorporates anti-tampering provisions, security and cybersecurity measures, enhanced market surveillance enforcement and a strengthened penalty framework. Under Article 3 (45), tampering is broadly defined to include disabling or modifying engine control systems, battery systems, OBD/OBM/OBFCM systems, odometers, software and logical control elements, and related data pathways.
At its core, EURO 7 reflects a regulatory realization: emissions compliance is inseparable from software integrity. As emissions-critical systems become software-governed, regulatory compliance structurally intersects with the cybersecurity governance framework established under UN R155, which remains essential for vehicle type approval.
Intersection of EURO 7 and WP.29
The intersection between Euro 7 and the WP.29 cybersecurity framework becomes evident when examining how emissions compliance is structured in software-defined vehicles.
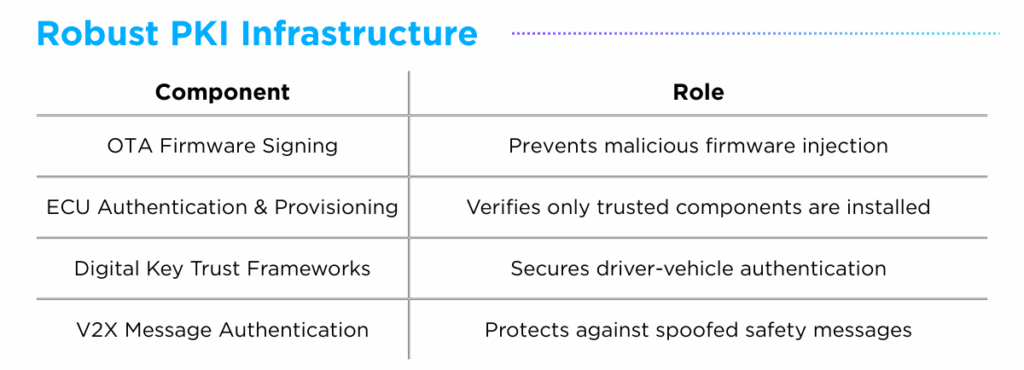
UN R155 governs software integrity within the WP.29 framework, and EURO 7 mandates long-term emissions and battery durability performance that depends on software-controlled systems.
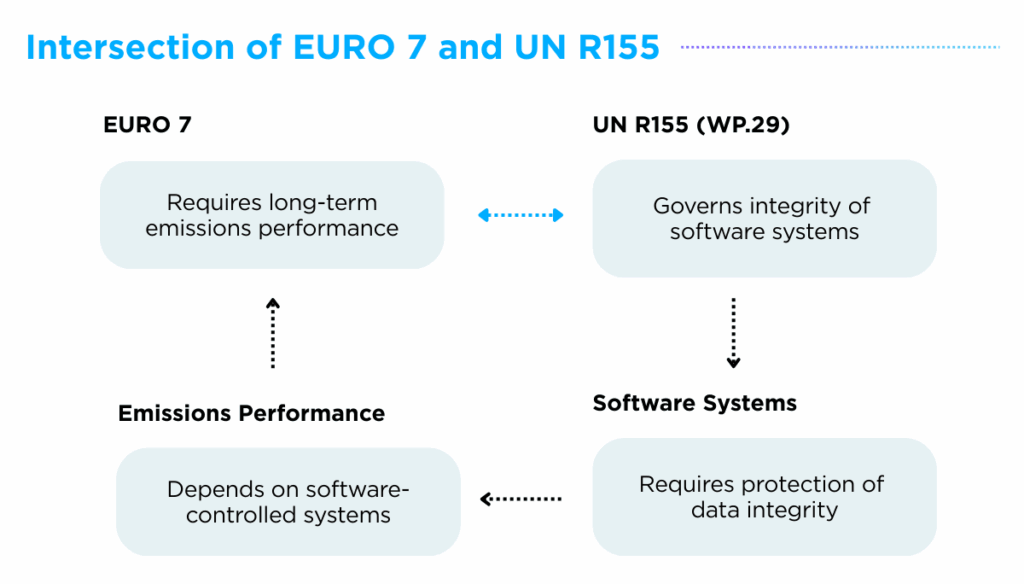
Together, these requirements establish a structural dependency in which sustained emissions compliance relies on effective cybersecurity governance.
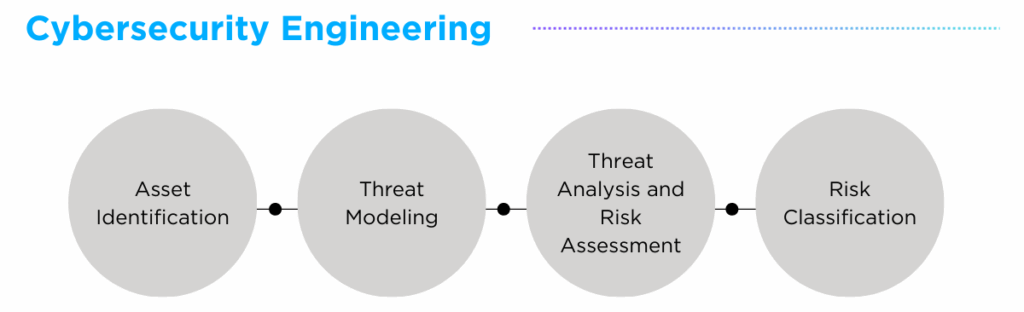
This dependency is not merely conceptual. It is reinforced through explicit references to UN R155 within EURO 7, particularly in relation to cybersecurity measures, security requirements, and Threat Analysis and Risk Assessment (TARA) obligations.
- Article 4(11)
- Requires manufacturers to ensure the secure transmission of emissions and battery durability data by applying cybersecurity measures in accordance with UN R155
- Annex XIV
- Defines anti-tampering, security, and cybersecurity requirements
- Incorporates UN R155 definitions of attacks
- Requires vulnerability minimization based on best available knowledge
- Mandates TARA processes that reflect EURO 7 objectives
- Provides conformity declaration templates for type approval submission
These provisions demonstrate that EURO 7 does not operate independently of the WP.29 cybersecurity architecture; rather it integrates cybersecurity governance directly into emissions-related compliance obligations.
III. Need for Digital Regulatory Convergence
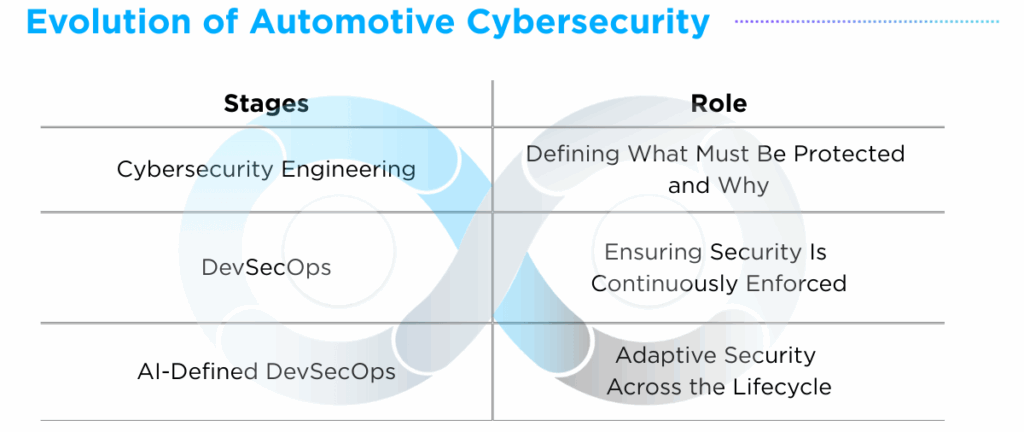
In a software-defined vehicle environment, emissions compliance depends on the integrity, resilience, and governance of digital systems. As vehicles evolve into configurable, updateable and connected platforms, the ability to demonstrate sustained compliance throughout the vehicle’s operational life becomes essential.
Manufacturers must therefore move beyond documentation-based certification toward engineering-based accountability. Emissions-critical systems must be cyber-resilient, monitoring data must be protected against manipulation and overall system architecture must be secure-by-design.
Within this regulatory landscape, the convergence of EURO 7 and the WP.29 cybersecurity framework establishes the need for integrated digital regulatory governance — aligning cybersecurity governance, environmental engineering and type approval strategy within a unified compliance architecture.
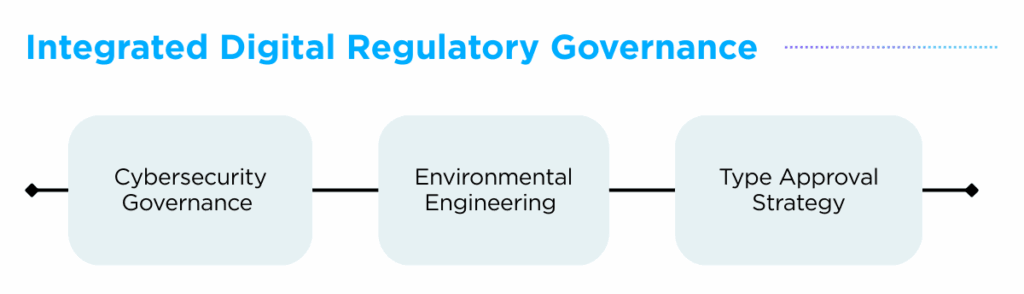
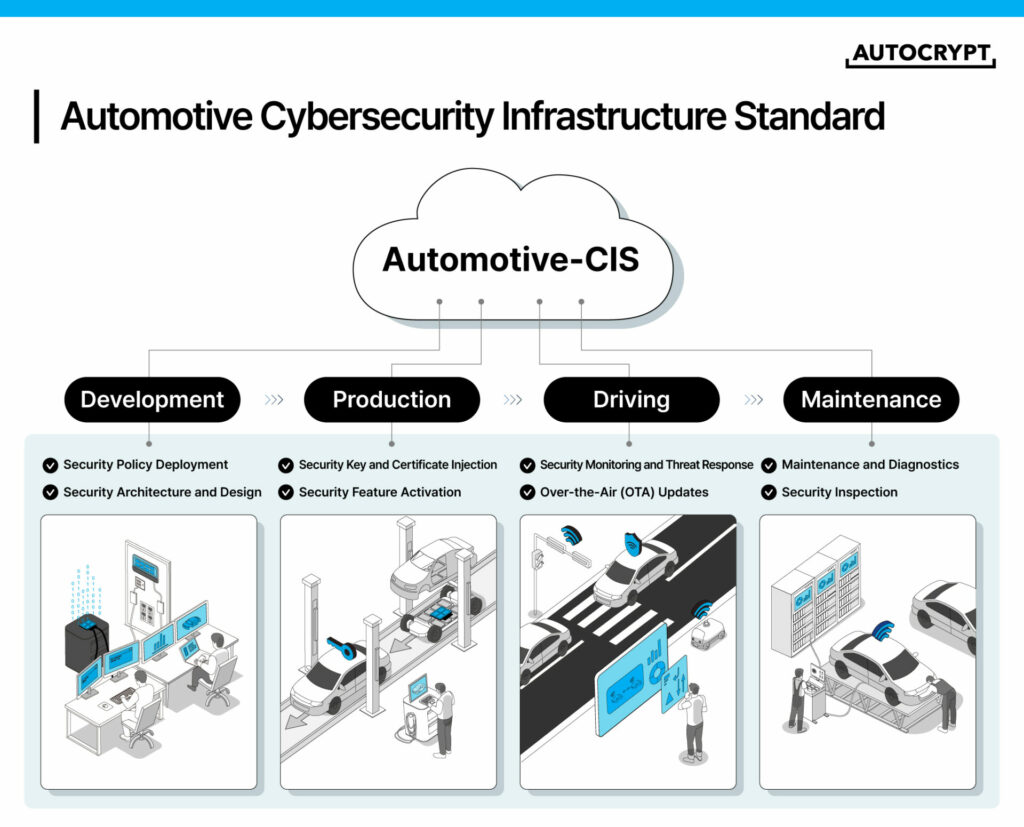
At AUTOCRYPT, we support OEMs and Tier suppliers in navigating this regulatory convergence. Through our WP.29 consulting services (Link), we support firms in establishing and optimizing UN R155 Cybersecurity Management Systems (CSMS), conducting AI-powered Threat Analysis and Risk Assessments (TARA), and integrating cybersecurity governance into emissions-critical system architectures under a holistic regulatory strategy.
Our objective extends beyond securing type approval. We help manufacturers sustain compliance throughout the vehicle lifecycle within an evolving regulatory landscape.
Additional Resources
- Learn more about our WP.29 Consulting Service: https://autocrypt.io/services/wp-29/
- Explore our WP.29 Whitepaper: https://autocrypt.io/downloads/abstract-white-paper-seamless-wp-29-implementation/
- To learn more about our end-to-end mobility solutions, visit https://autocrypt.io/
![[AUTOCRYPT] CES 2026 Themes](https://autocrypt.io/wp-content/uploads/2026/01/1222-D-14-2-2-e1768796696952-1024x498.png)
![[AUTOCRYPT] Solution Launch of Automotive-CIS (Cybersecurity Infrastructure Standard)](https://autocrypt.io/wp-content/uploads/2026/01/Blog-CES-2026-Highlights-2-e1768796899897-1024x573.png)
![[AUTOCRYPT] AI-driven automation across the DevSecOps process](https://autocrypt.io/wp-content/uploads/2026/01/3-e1768797215477-1024x561.png)
![[AUTOCRYPT] Public Perspectives on Future Mobility](https://autocrypt.io/wp-content/uploads/2026/01/4-e1768797322322-1024x415.png)